49
Connect Terraform to Azure Devops Git Repos over SSH
Terraform supports many different Module Sources. In todays tutorial we look at how we can configure an Azure DevOps repo with SSH and use this repo as a module source in terraform. We will also take a look at how we can use the install SSH key DevOps task in a pipeline that runs terraform so that the DevOps agent running the terraform deployment can connect to the DevOps repo as a source over SSH.
First we have to create a SSH key pair:
ssh-keygen. This will create a private key: id_rsa and a public key: id_rsa.pub under the following path: %UserProfile%/.ssh.ssh-keyscan -H -t rsa ssh.dev.azure.com > $env:userprofile/.ssh/known_hosts. The content of the file will be used later on in the setup of the Install SSH Key devops task in our DevOps pipeline.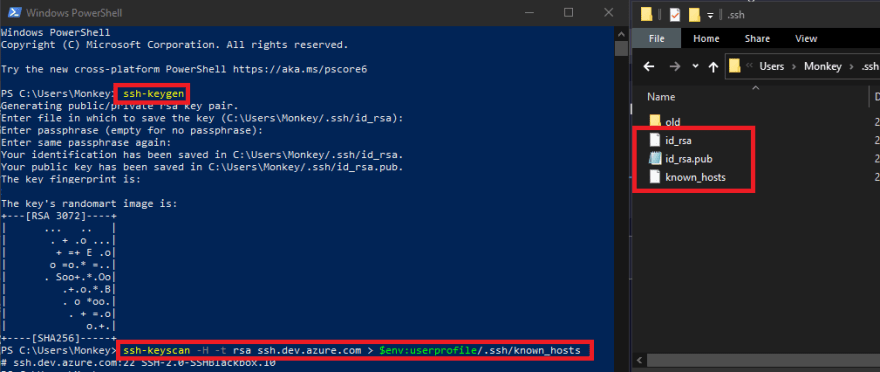
id_rsa into azure pipelines -> Library -> Secure files. The file can be renamed to make it more friendly to use later on in the Install SSH Key devops task. In my case I have renamed my private key to terraform_rsa.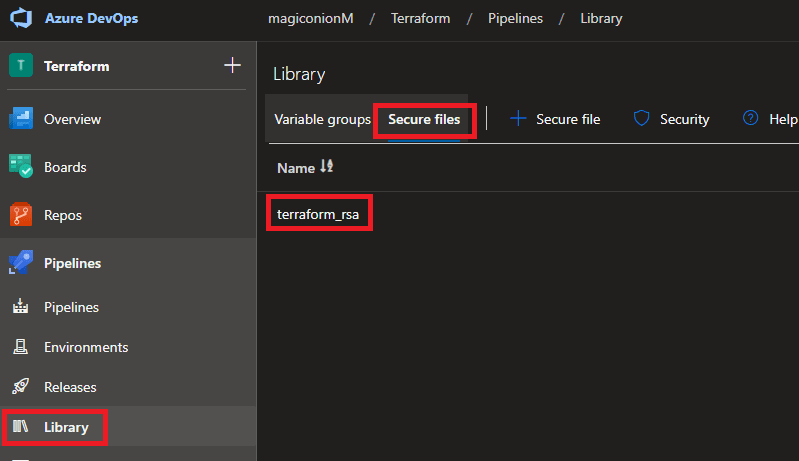
id_rsa.pub. In my case I have renamed my public key to terraform_rsa.pub.
When using an Azure DevOps pipeline to execute terraform code from a DevOps agent referencing an Azure Devops git Repo as a module source, we can make use of the Install SSH Key devops task to install the SSH key pair we just created onto the DevOps agent that will be executing the terraform code.
We will create a few variables next. These variables can either be created inside of a variable group or a key vault and accessed using the Azure key vault task in our devops pipeline.
terraform-git-ssh-pub and add the content of file id_rsa.pub. This can also be stored as a secret in Azure key vault instead and can be accessed as variables in our pipeline using the azure key vault devops task.git_ssh_known_hosts and add the content of file known_hosts created earlier with ssh-keyscan. This can also be stored as a secret in Azure key vault instead and can be accessed as variables in our pipeline using the azure key vault devops task.git_ssh_pass and add the secret value. This can also be stored as a secret in Azure key vault instead and can be accessed as variables in our pipeline using the azure key vault devops task.id_rsa)Thats it, the Install SSH Key Devops task will now install the SSH key on the Azure DevOps agent, allowing our terraform deployment to connect securely to our Azure DevOps git repo hosting our modules over ssh.
Here is a yaml pipeline example of the tasks/steps to read in secrets as variables from the key vault task and including the install SSH keys task.
steps:
### Link to key vault.
- task: AzureKeyVault@1
displayName: Keyvault
inputs:
azureSubscription: TerraformSP #ADO service connection (Service principal)
KeyVaultName: 'mykeyvault'
secretsFilter: '*'
runAsPreJob: true
### Install SSH key on ADO agent to access terraform modules git repo.
- task: InstallSSHKey@0
displayName: 'Install an SSH key'
inputs:
knownHostsEntry: '$(git_ssh_known_hosts)' #Variable pulled in from key vault via key vault task above.
sshPublicKey: '$(terraform-git-ssh-pub)' #Variable pulled in from key vault via key vault task above.
sshPassphrase: '$(git_ssh_pass)' #Variable pulled in from key vault via key vault task above.
sshKeySecureFile: 'terraform_rsa' #This was originally renamed from id_rsa and uploaded into secure files library on the project hosting our TF modules repoHere is an example of how we can reference our Azure DevOps repo containing our module code in our terraform deployment.
module "mymodule" {
source = "git::git@ssh.dev.azure.com:v3/Org/Project/repo"
}I hope you have enjoyed this post and have learned something new. You can also find the code samples used in this blog post on my Github page. ❤️
49

