40
CI with Snyk using GitHub Actions
GitHub Actions can be used as a CI tool for building, testing and deploying our code. With the aid of Synk, it can also automate the process of checking vulnerabilities.
Snyk is a developer security platform for securing code, dependencies, containers, and infrastructure as code.
It can be used in IDE such as IntelliJ, Visual Studio Code and so on as a tool to scan vulnerabilities in the code and librabries.
It can also be used to secure containers by finding and fixing issues in containers and continuously monitor container images.
It can also be integrated with CI/CD tool to find and fix issues in application continuously.
In this article, we will integrate Sync with GitHub Action, a CI tool from GitHub, in order to secure our application continuously.
It is required to submit Access Tokens to Snyk and Npm Registry for authentication when performing security check and publishing respectively.
Action Secrets are environment variables that are encrypted. It is useful to store sensitive information such as access tokens. Action Secrets can be used in Action Workflow file.

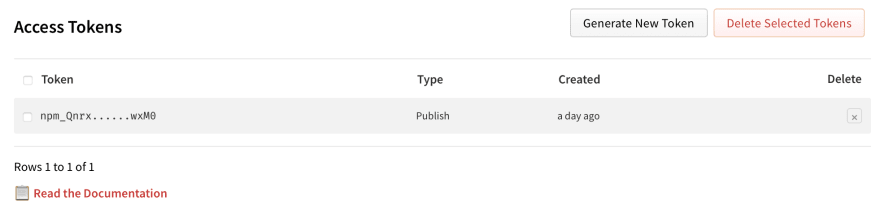
Login npm.
-
Click "Access Tokens" on the popup menu shown when the profile image is clicked.
-
Click the "Generate New Token" button on the "Access Tokens" page.
-
In the "New Access Token" page shown, select "Automation" from the "Select type" list, and click "Generate Token".
-
A new Token should then be generated. Copy the token for later use.
Login Snyk.
Click Account Settings > API Token section.
-
In the KEY field, click "click to show", then select and copy your token.
Create Actions Secrets NPM_TOKEN and SNYK_TOKEN for access to npm repository and Snyk respectively.
Login GitHub.
Click the target repository.
Select the "Settings" tab.
On the "Settings" page, select "Secrets" on the left navigation menu. "Action secrets" page should be shown.
Click the "New repository secret" button. A "New secret" page should be shown.
-
Input "Name" and "Value" of the tokens, and then click the "Add secret" button.
Name Value NPM_TOKEN { Access Token for NPM } SNYK_TOKEN { Auth Token for Sync }
A basic GitHub Action workflow file consists of 3 secions:
- name: Action Name
- on: How the action will be triggered.
- jobs: Jobs to be performed when the Action is triggered.
-
Update name section.
name: CI Publish, with security check using Snyk -
Keep on section unchanged. By default, the action is triggered when a push or a pull request occurs.
# Controls when the workflow will run on: # Triggers the workflow on push or pull request events but only for the main branch push: branches: [ main ] pull_request: branches: [ main ] -
Update jobs section.
There are 3 jobs that are set up in this Action:
i. security: Use Snyk to check for any vulnerability.
ii. build: This job is used to build the code. In this example, we build a Node.js application with various Node versions defined in an array. This allows us to test the application running on different Node versions in a very easy approach.
iii. publish: Publish the package to npm repository, allowing other developers to download and install the package, simple using the
npm insallcommand.To set up a job that depends on other job(s) to be run successfully,
needscan be used. For example,needs: [security, build]means that the job publish requires the jobs security and build to be executed successfully before it can be run. If either of the jobs fails, the publish job will not be executed.Here below list the entire workflow file:
# A workflow run is made up of one or more jobs that can run sequentially or in parallel jobs: security: runs-on: ubuntu-latest steps: - uses: actions/checkout@master - name: Run Snyk to check for vulnerabilities uses: snyk/actions/node@master env: SNYK_TOKEN: ${{ secrets.SNYK_TOKEN }} with: command: monitor build: runs-on: ubuntu-latest strategy: matrix: node-version: [10.x, 12.x, 14.x, 15.x] steps: # Checks-out your repository under $GITHUB_WORKSPACE, so your job can access it - uses: actions/checkout@v2 - name: Use Node.js ${{ matrix.node-version }} uses: actions/setup-node@v2 with: node-version: ${{ matrix.node-version }} - name: Install dependencies run: npm ci - run: npm run build --if-present - run: npm test publish: needs: [security, build] runs-on: ubuntu-latest steps: - uses: actions/checkout@v2 - name: Use Node.js uses: actions/setup-node@v2 with: node-version: '15.x' registry-url: 'https://registry.npmjs.org' - name: Install dependencies run: npm ci - name: Publish run: npm publish env: NODE_AUTH_TOKEN: ${{ secrets.NPM_TOKEN }} -
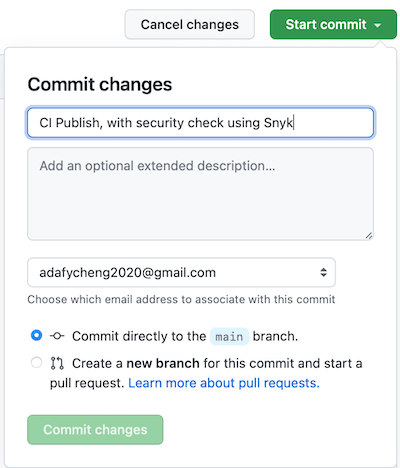
Commit the workflow file.
- Click "Start Commit" button on the left.
- Input description. It is better to input the Action Name, since it will be shown in the Action History.
- Click "Commit changes" button.
- Once the "Commit changes" button is clicked, the Action will be triggered to execute.
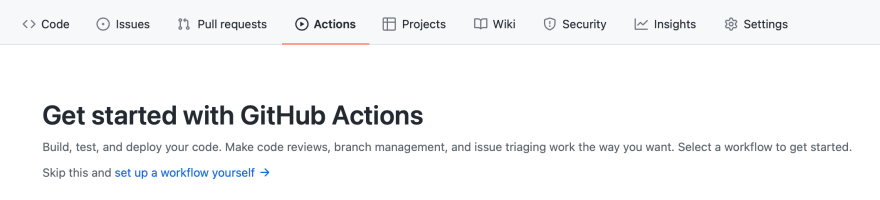
Our GitHub Action action can be triggered when the workflow file is updated, push or pull request occurs.
-
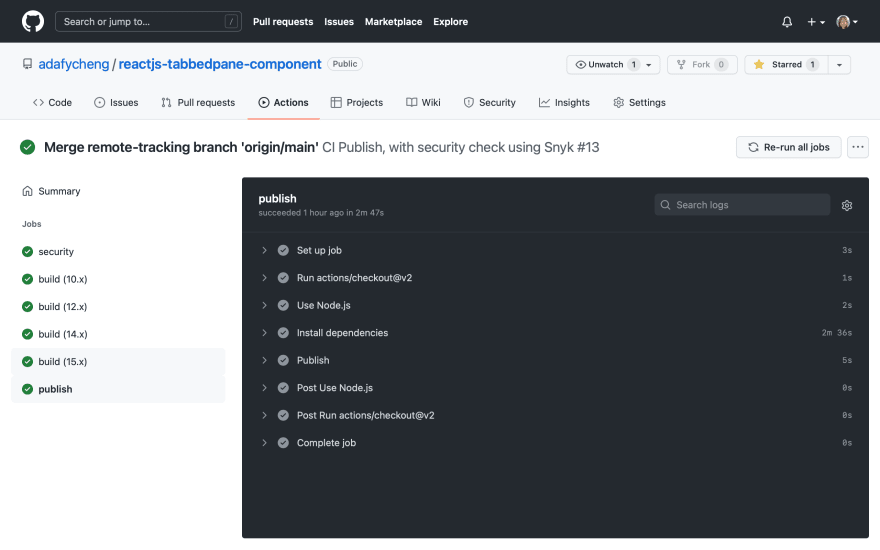
Once the Action is triggered, the defined jobs will be run.
-
Once the Action is completed successfully, a green tick will be shown.
-
Upon completion, check the security job details by clicking the security link on the summary panel on the left.
security: runs-on: ubuntu-latest steps: - uses: actions/checkout@master - name: Run Snyk to check for vulnerabilities uses: snyk/actions/node@master env: SNYK_TOKEN: ${{ secrets.SNYK_TOKEN }} with: command: monitorWith monitor command, the scan is performed and report is generated, but the process will not be interrupted. In other words, even if vulnerabilities are found, the job is finished successfully without error and next job will not be interfered and will then start.
To view the report, open the link stated as "Explore this snapshot at" in the result of "Run Snyk to check for vulnerabilities" section of the security job in a browser.
It is recommended to use the monitor command at the beginning to find the vulnerabilities during development stage. After the vulnerabilities are fixed or ignored, in production stage, we can then set to "synk test" command. This command will fail the builds when vulnerabilities are found. In this case, we can decide whether to stop or continue the build for production deployment.
-
Check the build jobs details by clicking the build link on the summary panel on the left.
-
Check the publish job details by clicking the security link on the summary panel on the left.
-
Check whether the package is published at npm repository.
Security vulnerabilities are subject to attack and should be closely monitored. By applying security scan during CI/CD Integration, our applications can be continuously monitored against security threats.
40